In recent years, Latin America has experienced rapid urban modernization through smart city projects that integrate video surveillance, artificial intelligence (AI), and automated management of public services.
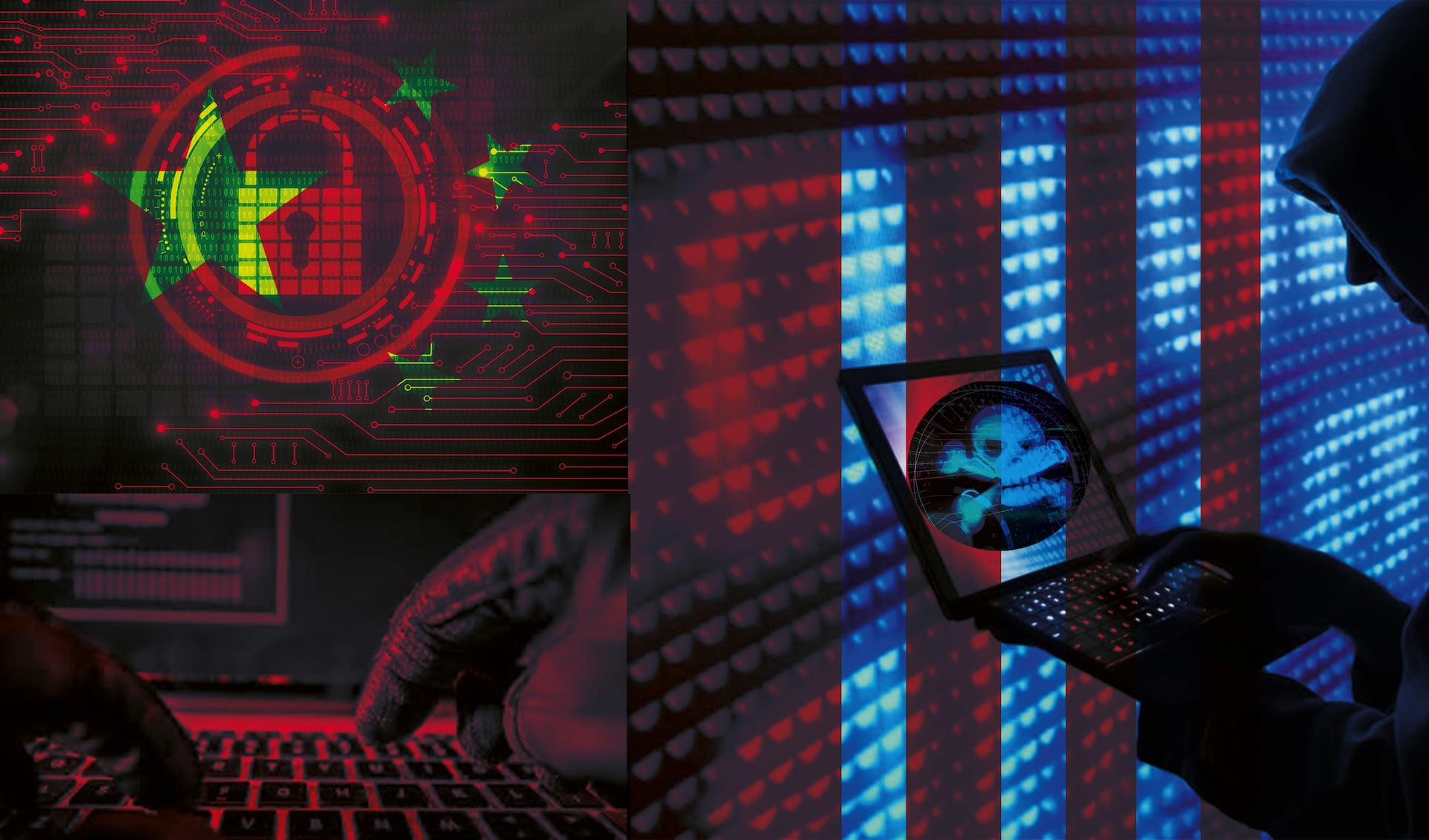
Although these initiatives promise greater efficiency and security, they have created a troubling dependence on technological infrastructure originating outside the Western Hemisphere, especially from state-linked entities like China, posing significant geopolitical challenges, facilitating foreign intelligence gathering, and complicating the fight against transnational criminal organizations (TCOs) and the defense of digital sovereignty.
Technological dependence and digital sovereignty
The Peruvian Army’s Center for Strategic Studies (CEEEP) warns that the proliferation of these technologies is part of a global strategy that seeks to consolidate economic and political influence through standardized solutions, increasing “regional vulnerability in terms of digital sovereignty.” This vulnerability is acutely exposed by the rapid expansion of Chinese state-linked technology in key urban and national infrastructure.
In practice, this means that large volumes of urban data — mobility, finance, public services, and behavior patterns — are controlled by external operators, which can directly compromise national and regional security.
Regional threats and cyberattacks
The challenge comes not only from TCOs but from geopolitical actors. A case in point is the infiltration in November 2024 of Paraguayan government systems by the Flax Typhoon hacking group, a Chinese state-linked espionage actor, illustrating the risks of intelligence and digital influence operations that can facilitate illicit activities on a transnational scale.
The Russian criminal group Conti also perpetrated a major ransomware attack in Costa Rica in 2022, which paralyzed more than 30 state institutions, crippling critical services, exposing sensitive data, and compromising surveillance systems. According to the BBC, some of the stolen information was published on the dark web, putting national security and citizens’ privacy at risk.
Countries such as Brazil, Mexico, Colombia, and Peru have also been frequent targets of cyberattacks from both state-linked groups and organized crime, including ransomware and data leaks, particularly in urban surveillance systems. Specific TCOs like the Tren de Aragua have also leveraged digital vulnerabilities, employing sophisticated ATM jackpotting schemes to hack bank machine operating systems and commit high-tech theft across borders.
Víctor Ruiz, founder of the SILIKN cybersecurity center in Mexico, warns that “this dynamic reinforces technological dependence and compromises digital sovereignty.” Ruiz highlights that access to information on “mobility patterns, infrastructure, and urban behavior gives companies strategic knowledge that could be used to expand their commercial presence or as a tool for geopolitical influence.”
Surveillance and technology concentration
Companies such as Huawei, Hikvision, Dahua, and ZTE, which operate under Chinese government mandates, have deployed video surveillance, AI, and 5G technology networks in key cities in Brazil, Colombia, Ecuador, Panama, and Peru. According to Access Now, an organization that defends digital rights worldwide, these systems collect enormous volumes of urban data — from real-time images to citizen habits —without guaranteeing compliance with international standards of transparency and security.
Access Now identifies these Chinese companies as the main providers of biometric surveillance in the region and reports that their technologies have been implicated in “human rights violations, affecting journalists, activists, human rights defenders, and vulnerable groups.”
This concentration of suppliers limits the ability of governments to audit and supervise these systems, a concern shared by many think tanks and experts.
National vulnerabilities and strategic risks
The integration of these platforms into critical infrastructure presents challenges for security and technological autonomy, often exposing nations to the strategic control of Beijing-linked actors.
In Ecuador, for example, the ECU-911 center operates with Chinese technology, which hinders interoperability with the security standards of partner countries and raises concerns over unauthorized data access.
Ruiz warns that “these technologies respond to regulatory frameworks defined by external actors, which complicates regional intelligence cooperation and facilitates the intrusion of criminal and terrorist groups.” For example, Chinese national security laws can compel technology companies to cooperate with state intelligence and security services, presenting a direct pathway for foreign intrusion and data extraction.
In Colombia, closed video surveillance and urban control systems limit technological autonomy. Reliance on Chinese systems means critical functions are vulnerable to remote disruption. “Failures or interruptions in traffic lights, cameras, and sensors could be used as leverage in political or contractual scenarios,” or be intercepted by organized crime for their fraudulent activities, Ruiz points out.
In Panama, the infrastructure adjacent to the Canal, equipped with Chinese technology, represents critical vulnerabilities due to Chinese-supplied port technology and digital infrastructure. Specifically, Chinese-made cranes and surveillance systems that are widely used in ports adjacent to the waterway. “Even brief interruptions could generate millions in losses,” Ruiz adds. This places one of the world’s most critical maritime choke points at risk of external influence or espionage.
In Brazil, the presence of Chinese suppliers in 5G networks and critical digital systems increases the challenges for cyberspace governance, creating massive vectors for unauthorized data transfer and control by organized criminal networks.
Toward the protection of digital sovereignty
Faced with these challenges, experts such as Ruiz urge Latin American governments to strengthen their regulatory frameworks, conduct frequent audits, and promote the development of local talent in cybersecurity and technology. “The lack of regulation on how data is stored or deleted increases uncertainty and risks,” Ruiz says.
The development of regional technology clusters and active oversight by defense and security ministries would significantly enable the region to take greater control of its strategic data without relying exclusively on foreign providers.
Through these measures, the Americas can effectively strengthen the protection of their strategic and citizen information, shielding their societies from the threats of organized crime and transnational influence in the digital environment.