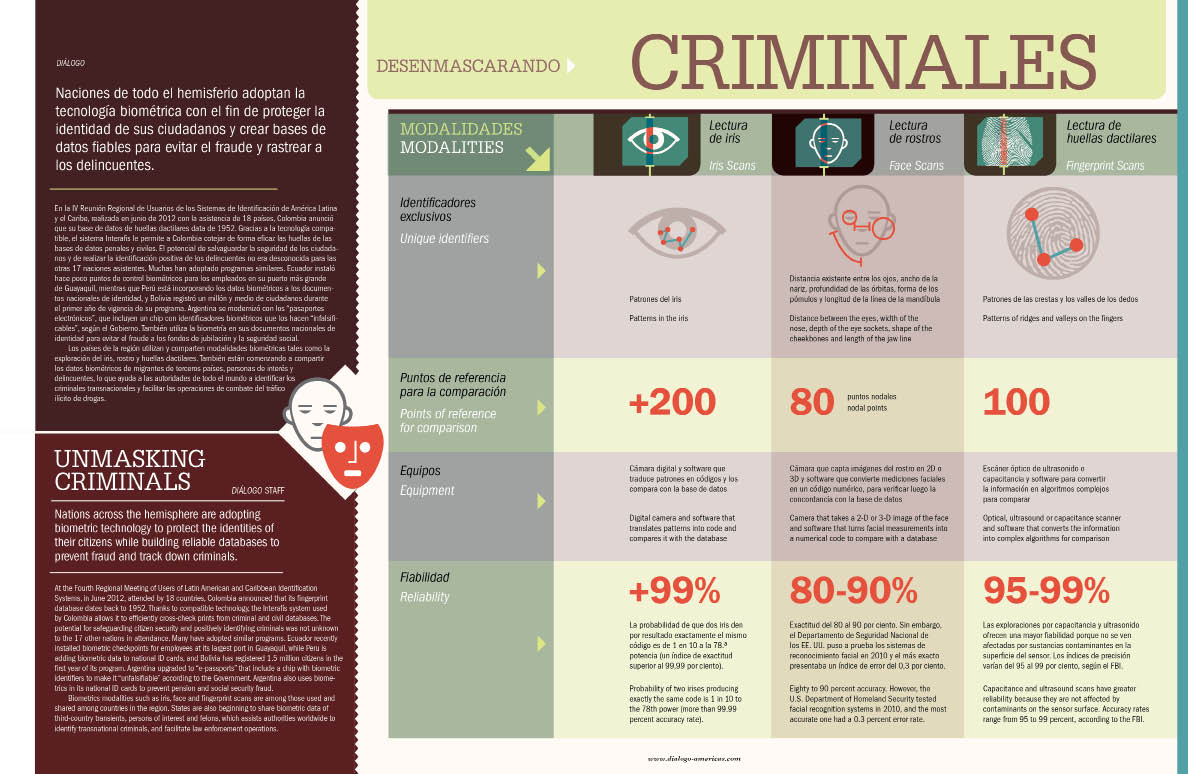
Nations across the hemisphere are adopting biometric technology to protect the identities of their citizens while building reliable databases to prevent fraud and track down
criminals.
Unmasking Criminals
January 01, 2013
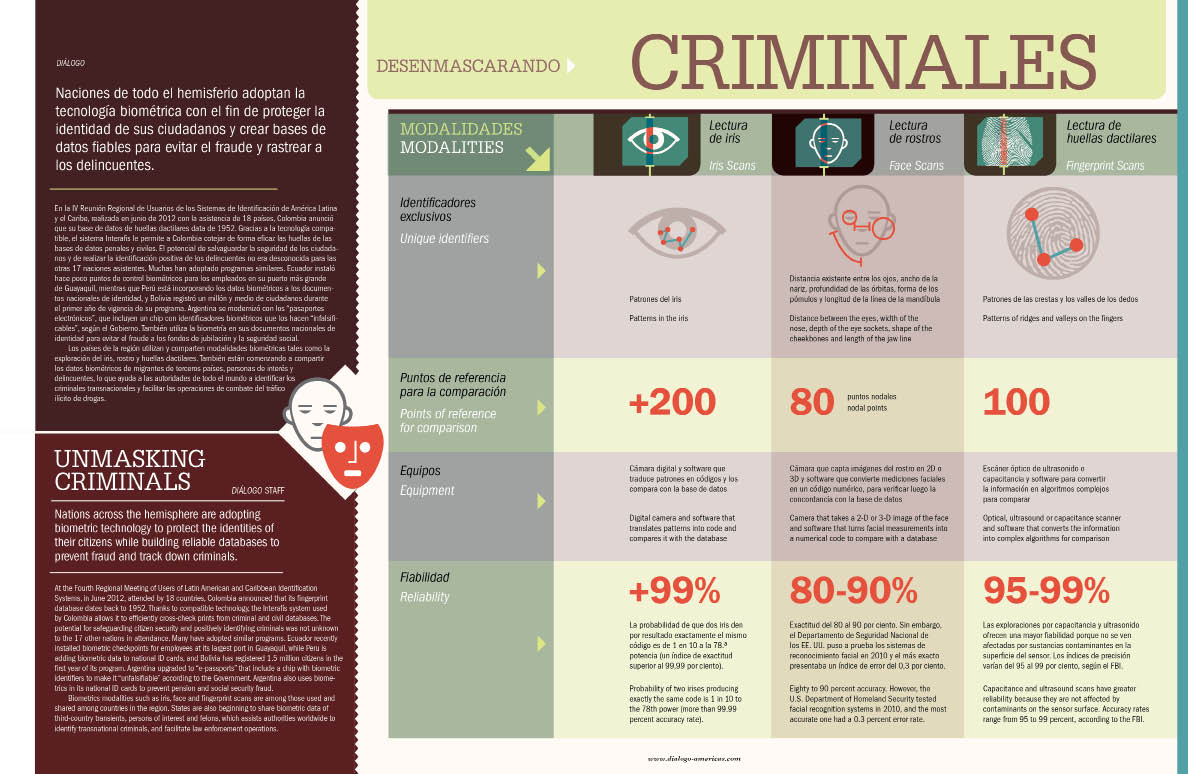
Nations across the hemisphere are adopting biometric technology to protect the identities of their citizens while building reliable databases to prevent fraud and track down
criminals.